I manage a bunch of internal servers and for those that aren’t part of the wider web I like to use key pairs to speed up my sign ins and maintenance.
Key-Based SSH Logins
Key-based authentication is the most secure mode of authentication usable with OpenSSH. Key-based authentication has several advantages over password authentication, for example the key values are significantly more difficult to brute-force, or guess than plain passwords, provided an ample key length.
Key-based authentication uses two keys, one “public” key that anyone is allowed to see, and another “private” key that only the owner is allowed to see. To securely communicate using key-based authentication, one needs to create a key pair, securely store the private key on the computer one wants to log in from, and store the public key on the computer one wants to log in to.
Here’s how to set it up.
There are two player roles:
- Host – this is the primary computer you sign in from.
- Target – the server you’d like to login to with a key
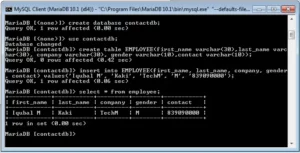
#1 Create all Users
If you are going to be using a specific user on both computers, make sure they are setup on both the host AND the target.
#2 Generate Keys on Host
Use this command to generate a strong key to use for connecting to the target. Leave all prompts blank when generating it.
ssh-keygen -t rsa -b 4096
#3 Copy Host Key to Target
ssh-copy-id <username>@<target>
#4 Setup Target Permissions
Set the permissions on the target server to:
chmod go-w ~/ chmod 700 ~/.ssh chmod 600 ~/.ssh/authorized_keys
#5 Test Login
ssh <username>@<target>
If the login fails, make sure the target supports SSH with keys. Look in the SSH config file for the following lines, they should look like this:
PubkeyAuthentication yes RSAAuthentication yes
Discover more from AJB Blog
Subscribe to get the latest posts sent to your email.